Introduction
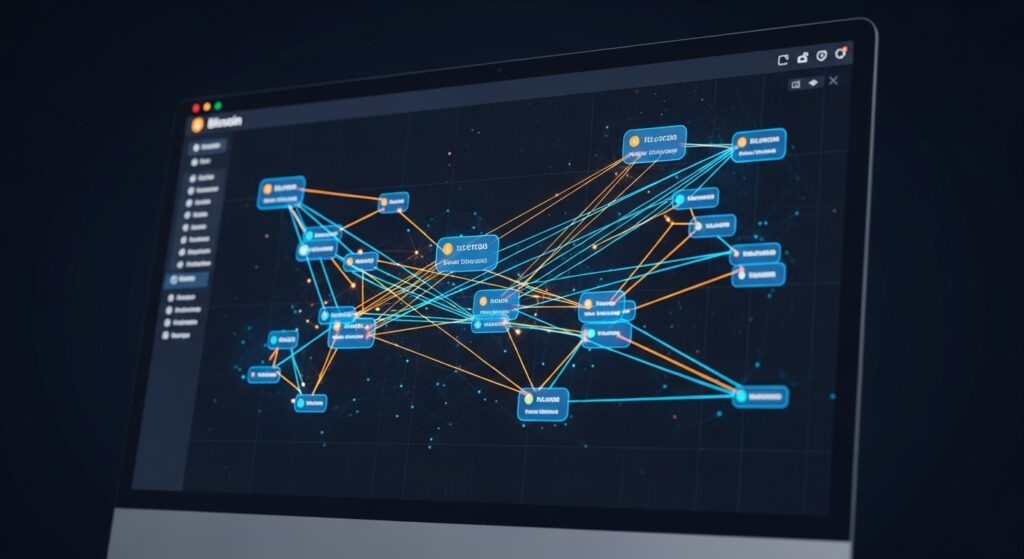
Bitcoin forensic analysis is the foundation of every successful crypto investigation. It involves tracking blockchain transactions, analyzing wallet activity, and identifying patterns that can reveal how funds move and where they end up.
As cryptocurrency fraud continues to grow, understanding Bitcoin forensic analysis is no longer optional. Investors, victims, and professionals all need to understand how tracing works to protect assets and respond effectively to suspicious activity.
This process is widely used by:
- Blockchain forensic analysts
- Cryptocurrency exchanges and compliance teams
- Law enforcement agencies
- Financial investigators
- Legal professionals
The goal is simple: follow the money, identify patterns, and determine whether real-world attribution and recovery are possible. Read our Guide crypto investigation guide
What Is Bitcoin Forensic Analysis?
Bitcoin forensic analysis is the process of examining blockchain data to trace transactions, identify wallet relationships, and uncover potential ownership or control of digital assets.
It combines:
- Blockchain transparency
- Analytical techniques
- Behavioral pattern recognition
- External intelligence sources
One key principle defines the entire process:
Transactions are permanent, but identities are inferred — not directly known.
Why Bitcoin Is Traceable
Many people believe Bitcoin is anonymous. In reality, it is one of the most transparent financial systems ever created.
Public Ledger Transparency
Every transaction is recorded on a public blockchain. This allows anyone to trace the movement of funds from one wallet to another.
Pseudonymity, Not Anonymity
Wallet addresses do not directly reveal identities, but they can be linked to real-world entities through investigation.
Immutable Records
Transactions cannot be altered or deleted. This makes blockchain data highly reliable for forensic analysis.
How Bitcoin Transactions Are Traced
Bitcoin forensic analysis follows a structured approach.
Transaction Identification
Investigators begin with:
- Transaction ID (TXID)
- Wallet address
- Timestamp
This process involves the use of advanced tools similar to ETHERSCAN: https://etherscan.io which enable our investigators to determine where the stolen Bitcoin has moved and whether it has reached a recoverable point.
Flow Mapping
Funds are traced from one wallet to another.
Analysts identify:
- Transaction paths
- Splitting and consolidation
- Movement patterns
Address Clustering
Wallets are grouped using heuristics such as:
- Common input ownership
- Shared transaction behavior
- Change address detection
This reveals whether multiple wallets belong to the same entity.
Behavioral Analysis
Patterns provide strong investigative signals:
- Repeated transaction sizes
- Timing patterns
- Address reuse
- Interaction with known services
Key Concepts in Bitcoin Forensics
Understanding these concepts improves accuracy and credibility.
UTXO Model
Bitcoin uses a UTXO system, where transactions consume previous outputs and create new ones. This allows precise tracking of funds.
Change Addresses
Unused portions of a transaction are sent to a new address controlled by the sender. Identifying these is critical for accurate tracing.
Dusting Attacks
Small amounts of Bitcoin are sent to multiple wallets to analyze spending behavior and identify connections.
Coin Mixing
Mixers are used to obscure transaction trails. While they complicate tracing, they do not completely eliminate it.
Wallet Fingerprinting
Different wallets and services have unique transaction patterns that can help identify their use.
Where Identity Is Revealed
Bitcoin forensic analysis becomes powerful when blockchain data connects to real-world systems.
Cryptocurrency Exchanges
Most exchanges require identity verification (KYC). When funds reach these platforms, attribution becomes possible.
Payment Services
Merchants and processors may store user data that can assist investigations.
Network Data (When Available)
In some cases, IP logs and service data can support attribution efforts.
Real-World Applications
Bitcoin forensic analysis is used in several key areas.
Scam Investigations
Tracing funds helps victims understand where their money went and whether action is possible.
Fraud Recovery
While not guaranteed, tracing increases the chances of identifying recovery points.
Compliance and AML
Financial institutions use forensic tools to detect suspicious activity and meet regulatory requirements.
Law Enforcement Cases
Authorities have successfully used blockchain analysis to track and seize illicit funds in major global cases. Read more
Limitations of Bitcoin Forensic Analysis
No investigation method is perfect.
Mixing Services
These are designed to disrupt traceability and increase complexity.
Cross-Chain Movement
Moving assets across blockchains reduces visibility.
Privacy Coins
Some cryptocurrencies are built to hide transaction data, limiting forensic capabilities.
Jurisdiction Issues
Even when funds are traced, recovery depends on cooperation from platforms and authorities. follow our full guide Recover stolen crypto assets
Case Example: From Transaction to Exchange
A victim sends Bitcoin to a fraudulent platform.
Within minutes:
- Funds are moved across multiple wallets
- Transactions are split and recombined
- Assets are consolidated
Further tracing reveals the funds were sent to a cryptocurrency exchange.
At this point:
- The exchange is identified
- A report is submitted
- A freeze request is initiated
If acted on quickly, there is a possibility of stopping withdrawal.
This type of case reflects real investigative workflows.
When to Seek Professional Help
Bitcoin forensic analysis can become complex quickly.
You should consider expert support when:
- Funds move across multiple wallets
- Attribution is unclear
- Large amounts are involved
- Time is critical
Professional investigators use advanced tools and structured methodologies to improve outcomes.
For expert Bitcoin forensic analysis and crypto investigation support, visit:
https://cryptorecoveryminions.com
Final Disclaimer
Bitcoin forensic analysis provides insight into transaction flows and potential attribution. However, recovery is not guaranteed.
Outcomes depend on timing, traceability, available data, and cooperation from involved entities.